Source control providers
If you are on an Enterprise plan, you can connect your source control to offer continuous validation and delivery of your APIs, reference docs, and developer portals.
From the Source control providers page, you can configure settings for:
- You will need an Enterprise-level Redocly plan to connect to GitHub Enterprise, Azure or Bitbucket self-managed.
- You will need a Pro Redocly plan to use GitLab self-managed.
GitHub Enterprise
Using Workflows, navigate to Settings > Source control providers.
On the Source control providers page, under GitHub Enterprise, complete the details to connect to your GitHub Enterprise account.
Select Save Github Enterprise Settings to save your changes and connect your account.
Once you have connected your account, it works similar to the GitHub integration source.
Azure
You will need the Professional or Enterprise plan to connect to Azure Repos connection.
Connect Azure Repos to Redocly
Redocly integrates by using a personal access token to authenticate to Azure Repos.
We recommend using a service user account. A service user is a user created in Azure Repos intended for use by a machine. You would log in to the service user account to generate a personal access token for use by a 3rd party service (like Redocly). We recommend naming your service user "Redocly" or similar.
Log into your Azure Repos account, and under User Settings, create a personal access token. For more information, read the Azure docs to learn how to create a personal access token. Azure DevOps has a current and preview features environment which have different locations for finding where to generate your personal access token.
Set permissions for the personal access token.
- Select
custom definedscopes.You must define the scopes correctly.
- Set
read & writecode access. - Set Web/Service hooks permissions.

If you set an expiration on the personal access token, set yourself a reminder to generate a new token.
In Redocly, navigate to Settings > Source control providers page.
Scroll down to the Azure section of the page, and complete the details.
- Enter the Organization name as it appears in your Azure account.
- Enter your personal access token you created in Azure Repos.
- Select Save Azure Settings to save your changes.

You've now connected Azure Repos to Redocly.
Update access token
To update your token:
On the Source control provider page, under Azure, select Change.
Add in your new token, and select Update Azure Settings.

Disconnect Azure
To disconnect the integration between Azure Repos and Redocly, on the Source control provider page, under Azure, select Disconnect Azure.
Self-managed GitLab
Connect GitLab self-managed to Redocly
GitLab self-managed operates similarly to the GitLab.com integration, though it requires some additional setup.
Create a GitLab application
Navigate to your GitLab user settings and create a GitLab Application.
A regular user account is acceptable, but we recommend you create a service account for managing applications. Service accounts typically have administrative privileges, and are not used by human users, but by the system for administration and interacting with external services.

Go to the Applications tab and:
- Enter "Redocly Workflows" for the new application name.
- Set the Redirect URI to
https://app.redocly.com/callbacks/gitlab-auth. - Activate the api scope from the Scopes list in order to allow Redocly to read your repositories and write commit statuses.

Select Save application to create a new application.

You will be redirected to the page with credentials for the new application.

Keep this tab open as this data is required for the following steps.
Connect application to your organization in Redocly's web app
Using Workflows, navigate to Settings > Source control providers page.
Scroll down to GitLab self-managed section and copy/paste Application ID and Secret values from the GitLab application to the corresponding form fields. Also provide the URL to your self-managed instance.

Select Save self-managed Gitlab settings to complete the configuration.
Finish the authorization flow in a separate tab in your GitLab self-managed instance.

You're all set! You can now use the GitLab self-managed source similarly to the GitLab.com integration source.
Self-managed Bitbucket
You can use Bitbucket Server or Bitbucket Data center as a source for your API versions, reference docs and developer portal projects.
Connect your Bitbucket self-managed account to Redocly
Navigate to Settings > Source control providers.
Scroll down to the Bitbucket self-managed section and:
- Enter the Username and Password of your Bitbucket user account into the corresponding fields.
- Provide the URL of your self-managed Bitbucket instance. The URL must start with the protocol (either
httporhttps).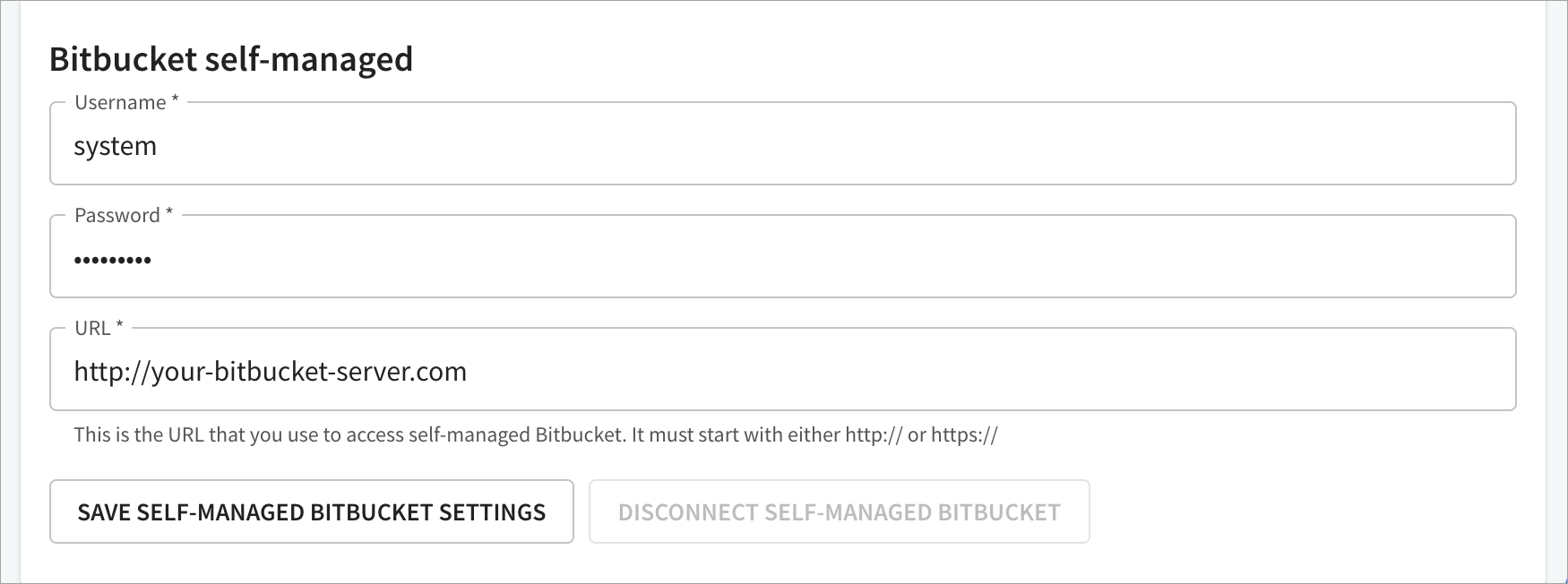
Bitbucket service accountsA regular user account is acceptable, but we recommend you create a service account on Bitbucket with access to desired repositories. Service accounts typically have administrative privileges, and are not used by human users, but by the system for administration and interacting with external services.
Select Save self-managed Bitbucket settings to complete the configuration.